mytest



![]()

UPDATES ON TWITTER: arudoudebito
DEBITO.ORG PODCASTS on iTunes, subscribe free
Hi Blog. With the rerelease of an article I wrote last year (I am reading all my old articles in order for the Debito.org Podcast, so listen here or read it here) is a revisitation of an argument I made about the next-generation “Gaijin Cards” (Zairyuu Kaado), with imbedded IC Chips. I expressed a fear that these “smart cards” will be remotely scannable, meaning the NPA will be able to zap a crowd and smoke out who’s foreign or not (whereas Japanese citizens have no legal obligation to carry ID 24/7 backed up with criminal punishment) — or will further justify racial profiling of people like me who look foreign but aren’t.
Techie Eido Inoue, a naturalized J citizen himself, writes here on invitation to address this argument. He was worried that this topic might get a bit geeky (he has in fact made it very readable, thanks), but never mind, this needs to be discussed by people in the know. However, please do read or page down to the end, where I have some basic counterarguments and a scan of something I saw the other day in a travel shop — a “scan proof” pouch for your valuables on sale! Read on.
//////////////////////////////////////////////
EIDO INOUE WRITES:
There has been a lot of concern these days about the inclusion use of NFC (near field communications) technology, which is a type of RFID (radio frequency identification), being included in the successor to the Japanese ARC (alien registration card), the 在留カード {zairyū kādo} (non-Japanese residence card). In this comment, I’ve summed up, per Debito’s request, some of the back and forth Q&A that has been occurring on other blogs:
Q: What sort of wireless technology is in these new cards? Is it reliable? Is it proven?
A: The card’s IC chip will use JIS X 6322 type B standards, which is basically the Japanese translation of ISO 14443 type B standards. This is the exact same international standard used for both Japanese and overseas e-passports, as well as Japanese driver’s licenses and the 住基カード {jūki kādo} (Japanese citizen residency card).
Q: What will be inside these chips?
A: The same information that’s printed outside the card:
* full passport/English legal name, date of birth, sex, nationality & domicile/state/locale
* resident address in Japan
* [visa] status, and status length / expiration date
* visa status grant date
* residency card number and expiration/renewal date
* work restrictions, if any
* any permitted activities outside of visa status
* color photograph
Special Permanent Residents, however, will only have the following on their cards:
* full passport/English legal name, date of birth, sex, nationality & domicile/state/locale
* resident address in Japan
* special permanent resident number and renewal date
* color photograph
Technically speaking, the 在留カード {zairyū kādo} (non-Japanese residence card) will be called and labeled as a 特別永住者証明書 {tokubetsu eijūsha shōmeisho} (Special Permanent Resident Identification [Card]) for people with this status.
[ the only thing that will not be on the chip but on the outside of the card will be the Ministry of Justice’s seal. Note that there’s much less information on this card than the ARC: no passport info, head of household, employer, etc. ]
Non-Japanese that have kanji names with their governments will have the kanji on the cards. In the case that the kanji is Chinese Simplified or Traditional and can’t be represented with using Japanese character sets, it will be converted to Japanese form.
[it was not clear from the literature I read what characters were permitted and what were not and what underlying character set encoding, such as JIS X 0208 or Unicode, would be used. It was also unclear to me from reading the literature as to whether non-Japansese without official government registered Kanji names, such as Japanese-Americans or those who just want a Kanji (or kana or hybrid) name, even if it’s 当て字 {ateji}]
Customs/airport officials plan to register / use the alphabet passport form and not the Kanji [even if it’s Japanese] form of the name as inputting / copying the kanji name takes too much time.
Unlike the previous ARC cards, there is no plan to list aliases (either katakana or kanji).
[It does not say how non-Japanese, who have Japanese aliases for anti-discrimination or other purposes, will prove what their registered legal alias is]
Years on the card will be specified in Western (ex. 2010) system, not Japanese (ex. H.22 or 平成22) system. Dates will be in Y M D order, and the fields will be labeled [so you know which is the month and which is the date]. Sex will be specified with a “M” or “F” [as opposed to 「男」, 「女」, 「♂」, or 「♀」].
[This should make the card more comprehensible to non-Japanese officials if you attempt to use it as ID overseas]
If a full name is too long for one line, it will be broken into multiple lines.
[better than the ARC and the Japanese driver’s license, which continued long (ie. Brazilian) names onto the back of the card]
Q: If the information inside the chips is the same as the information written on the outside of the card, what’s the point?
A: Three main points:
1. reduction of data entry errors (no hand copying the info from the card to some other system)
2. speed of processing (depends on the operator, processes, & hardware/software implementation)
3. [primary official reason] preventing the creation of completely bogus identifications using high tech printing, copying and manufacturing technology that is available to even amateurs today.
The info on the chip is digitally “signed” (a certificate validating that no information has been added, changed, or deleted) using PKCS (public-key cryptography standards). So long as the signing key is kept secure by the government, it’s mathematically impossible to recreate a government’s digital signature/certificate associated with a bogus identity. Now, you can clone (that is, copy the certificate along with the entire ID, including the photograph, without adding or removing anything) a digital ID. But that’s not the purpose of the certificate. The signature prevents somebody from creating a bogus ID from scratch. These days, thanks (?) to advances in technology accessibility, most professional and even some amateur forgers can create a phony identity card (“Taro McLovin”), mimicking holograms, blacklight ink, microprint, etc., that is so good it can fool a professional trained inspector.
But even the most powerful governments in the word have yet to break the modern strength digital signature/certificate algorithms — because the best mathematicians, working for the best spook agencies (NIST, NSA) in the world, created the system based on principles of impossible to solve quickly mathematics (ie. using ultra large prime numbers), then publicized all their work to have it checked by the other best mathematicians in the world. Based on what mathematicians have known for literally thousands of years, and taking into account the current state of Moore’s Law, the crypto should theoretically be safe from brute force attack for literally eternity. Where things fail is due to errors in implementing the algorithms, or theft/discovery of the secret keys, not in the algorithms themselves.
Anyway, for IDs with digital signature certificates, the forger is going to have no choice but to clone, in its entirety, somebody’s existing digital ID when they make a fake ID. Which means they’re going to have to look an awful lot like the person whose identity they stole because the picture data is calculated with the certificate’s hash. Plus they’re going to have to hope that the identity theft victim didn’t report the ID as stolen / lost or that the victim unknowingly had their ID scanned in a place that would be logically impossible for a followup scan of the cloned card. For example, a digital ID gets scanned in Hokkaidō, then the exact same digital ID with the same serial number gets scanned by another police officer in Fukuoka 5 minutes later; a computer will pick up on that.
Now, if there’s a fingerprint encoded in the chip (which is not the case for Japanese passports or the 在留カード {zairyū kādo} but is true for new European passports) and digitally signed, then even if the fraudster looks like the victim in the digitally signed photograph, they’re out of luck. They can’t remove or change the fingerprint without invalidating the certificate.
Q: Can a civilian or official read my card from a distance?
A: Extremely doubtful. The way the cards work is that while they have no power source of there own; they are powered by a minute amount of power they induce from their radio frequency for no more than a fraction of a second, and this power gives them the strength to produce a very faint signal that can only be practically read reliably by another device that’s less than four or 5cm away. The chips contain power regulators, so even if you send an extra strong signal to the chip in an effort to give the chip more power to work with, it does not produce a stronger return signal.
This is why you can see a lineup of Suica/Pasmo/Icoca/PiTaPa electronic wicket gates in a train station: the radio waves produced by those gates, which are no more than a meter apart, are so faint that each gate can’t hear and interfere with the radio waves being produced by the gates right next to it.
The maximum field range of a ISO 14443 device is less than 10cm. The maximum range that professionals have managed to get out of a ISO 14443 device in a laboratory (meaning neither the card or the reader can move for a long time, the room’s air is shielded from radio noise, and the lab’s using a very nonstandard reader) is 20cm: the length from the tip of your little finger to the tip of your thumb on an average outstretched hand.
Because the return signal from the chip inside the card is constant no matter how how power you throw at it, the only way you’re going to increase the range is by using a larger antenna. But even then there are limits, as the signal is so weak that it’s literally drowned out by the radio noise that permeates the real world.
Some professionals have speculated that, given a large enough (a very non-portable antenna; it would need to be mounted and not hand held), it is possible to increase the maximum range of ISO 14443, in a laboratory (not real world) setting, to 50cm: the length from your wrist to your elbow.
Anything longer than 20cm is suspect; anything longer than 50cm is science fiction, in my opinion.
Q: Could a crowd of people (assuming they’re in range of a reader), or even a whole bag of cards, be scanned en mass?
A: Even if it was possible to read ISO 14443 cards from a distance, ISO 14443 is designed to only work with one card at a time. It is not possible to have one reader read multiple cards, have many readers read one card, or have many readers read many cards.
It’s a matter of laws of physics (two signals being in the exact same frequency) and the way the devices were designed. Mobile phones, Bluetooth, and WiFi have very sophisticated and complicated protocols to allow them to share and operate and be individually addressed in a range of airspace, jumping and across (sometimes thousands) of frequencies and channels, sometimes using more than one simultaneously, in an elaborate cooperative ballet to prevent two devices from using the exact same airspace at the same time.
ISO 14443, on the other hand, not only doesn’t have these protocols, but in fact was specifically designed to not share airspace with anything else. There are specific fail-safe parts of the protocol that are designed to make the card/reader shut down, back out, and shut up if it detects something else using its airspace for safety/reliability reasons. It also has safety procedures to handle cases where it doesn’t have enough power or a good enough signal to complete a transaction: Everyone knows it’s futile to try to yank away your payment card or try to swipe your card for only a split second in an effort to fool the vending machine into making a transaction without having your balance debited.
If you’ve ever had two Suica Cards and/or a Japanese driver’s license in the same wallet, you know that the readers will refuse to work or will only work with one card. Again, this is not just a limitation of the technology, it is by design.
Q: But what if somehow somebody comes up with way that allows for eavesdropping of a card talking to a reader (from afar or near)? Am I safe?
A: Some people on the Internet have claimed even farther ranges than what we mentioned above: such as detecting the presence of a signal at 20 meters and actually discerning the digital bits at 10 meters. None of these claims have been independently confirmed or verified, and even if we give them the benefit of the doubt and believe for the sake of argument that it’s possible, nobody has shown they can break the cryptography gleaned from real devices in the field in real world situations.
To an eavesdropper, most ISO 14443 cards “sound alike.” This means they all — be it your e-passport or your U.S. Passport Card or your Japanese driver’s license or your FeLiCa based Suica/Pasmo/Icoca/PiTaPa or your PayPass credit card or your Japanese Taspo tobacco age-verification card — talk on the same frequency (13.56 Mhz). Furthermore, the transaction that occurs between the reader and the card is encrypted, so even if a bad person had such a clear signal that they were able to discern the individual digital bits going back-and-forth between the reader and card, it would be useless for determining the payload or even the type of card being used in most cases.
Thus, just because the card, either in your hand or concealed in a wallet, of you or the person next to you is or isn’t “ squawking” and you are or are not doesn’t mean somebody can figure out that “that person is a foreigner and that person is not” due to the presence or absence of a 13.56 Mhz encrypted squawk. That squawk could be anything, from a Japanese passport to a London train commuter Oyster Card.
NOTE: Some security journals have speculated that it may be possible to perform literally a “man-in-the-middle” attack in some cases. This means putting something physically between (the 10cm) space of air between the card and the reader that is big enough to ensure that the reader and card can’t hear each other; the bad spy device acts as a “relay” between the legit card and reader. So when you swipe, you should be absolutely sure you’re swiping the real legit reader and not something placed directly on top of it.
Q: Even if they can’t read the contents of my card, can a civilian or official detect that I’m in possession (or that I’m not in possession) of a 在留カード {zairyū kādo} (non-Japanese residence card) without my knowledge?
A: No. The reason for this in answered both in the previous question and the following question. You could easily fool an eavesdropper into thinking you swiped any arbitrary ISO 14443 Type B card that uses encryption by simply using another, completely different and unrelated ISO 14443 Type B card. You could purchase and carry your own battery powered USB portable [dummy] reader in a purse or bag, for example.
Q: Can a civilian or official read my card without my knowledge if they’re very near or next to me?
A: Japanese [and U.S. and E.U., but not all countries] e-passports, and yes, the new 在留カード {zairyū kādo} (non-Japanese residence card) have BAC (basic access control).
This means you have to know some piece of information that’s either on the card or in your head to read it.
Even if somebody manages to covertly (say, on a crowded train or bus) get a portable skimmer close enough [less than 10cm] to your back pocket, purse, bag, or briefcase to pick up your card, they still need to know some things that are on the card in order to read it.
NOTE: Not all NFC cards and RFID use this extra access control and/or encryption. So you don’t want to carry all your cards unprotected / unshielded in your back pocket. It is possible to obtain special, practical shielded slips for ISO 14443 based technology (tin foil hats sold separately). Some ISO 14443 technology (such as many, including Japanese, passports) already include a shielding envelope or technology integrated into the device. However, the presence of the shielding does not mean that the shielding is the last or only or even best line of defense against skimming; it is merely one component in a suite of many security components for the passport & residency card, already built-in by design, that would have to be compromised. To stay on topic, the NFC cards which are the discussion of the Q&A, such as Japanese passport, driver’s license, and yes, the 在留カード {zairyū kādo} (non-Japanese residence card), do implement and enforce BAC in addition to encrypting their point-to-point sessions with the readers.
Q: Can private enterprises read the IC chip?
A: Yes. The MoJ [Ministry of Justice] plans to publish the specifications for reading information from the card. However, they can’t override BAC (see above) which means a private enterprise would not be able to read your card without your knowledge.
[ This is interesting. The literature I have specifically mentions that society, especially financial institutions and mobile phone companies, needs a reliable domestic photo id for non-Japanese residents. ]
Q: What if the chip isn’t working? What if the private enterprise doesn’t have a reader? Is there an alternative electronic way to verify the card without the chip? Will I be hauled off to the police box if my chip isn’t working?
A: The MoJ [Ministry of Justice] is also going to make a website available for checking cards (which presumably could be accessed by even mobile phone browsers). The website will accept the card’s number and one other piece of information from the card to prevent people from randomly guessing 在留カード {zairyū kādo} (non-Japanese residence card) numbers. The literature suggests that this extra information be the card renewal/expiration date.
Upon submitting the number, the website will simply return 有効 {yūkō} (valid) or 失効 {shikkō} (invalid). To protect private information, no other information (such as name, date of birth, nationality, visa status, etc.) will be returned.
ENDS
/////////////////////////////////////////////////////////
COMMENT FROM ARUDOU DEBITO (donning his tinfoil hat):
One conflict I always notice from my side of the spectrum is the inherent mistrust of scientists — when they claim a new technology, open to all manner of theoretical abuses, is “safe”. This is the same camp that tends to blame the scientists on the Manhattan Project for opening Pandora’s Box with The Bomb.
Continuing in that vein in an attempt to contrapose aarguments to Eido’s research above, a whole bunch of “what ifs” and “whys” that are not all that unreasonable quickly come to mind:
1) WHAT IF the sacred encryption keys get cracked or leaked somehow? Can happen quite easily, if not in part due to government error, see here. And hackers are forever getting increasingly sophisticated. It’s hard to imagine the “eternity” scenario in a place when it’s techie vs. techie, and one is but a few steps ahead of the other. The risk is too great — once the door is open, identity theft becomes possible.
2) WHAT IF the realm of “science fiction” becomes “science fact”? We once thought manned flight (with or without gravity), or portable computers, or even gigabytes of data stored in tiny places were impossible, but technology, again, has a habit of catching up and deleting the “im” prefix. Encryption notwithstanding, decrypting computers are getting faster and smarter all the time.
3) WHY are foreigners only required to be IDed by private businesses (last two Qs above)? Actually, I can answer that one. Because the NPA feels the irrepressible need to track people that could commit crime. And because they can’t do that to Japanese citizens due to the outrage — witness the flop of the Juuki Netto system. People just don’t want to be forced to carry ID in this society, much less tracked by it. It’s just happening to foreigners because they can’t stop it. And it increases the Japanese police’s power by deputizing the private sector. This is just common sense — give the police anywhere in the world extra power, and they will feel fully justified in using it to accomplish their goals until they’re told they’ve gone too far (and in Japan, they insufficiently are).
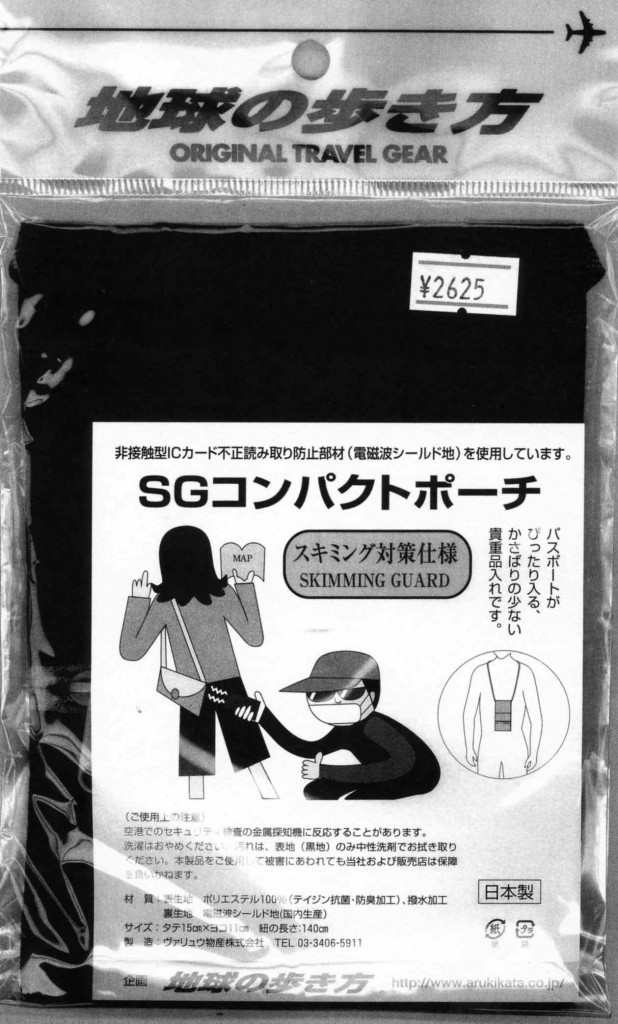
4) WHY is that same private sector now advertising preventative measures against RFID technology? Check this out — a scan-proof pouch for your valuables now on sale in travel shops in Japan (seen because I went and renewed my passport on Tuesday):
Unless this is Snake Oil (and Eido himself points out that non-contact scanning is possible), how do we deal with this? By saying that the distance is too small or the definition of the signal is too vague to matter? Again, I will raise the technology argument to say that once the leap is possible, it’s only a matter of degree. This may be tinfoil-hat-ism, but to me it’s like saying, “Don’t worry about The Bomb; if there is fallout from an unlikely attack, there are anti-radiation pills you can take.” Sorry, I don’t believe in having to put the Genie back in the Bottle. Especially since the reasons for this measure are less a technological inevitability than a political necessity (i.e., tightened policing of the only people you can police this way, since society in general wouldn’t dare accept it). If this is scary enough to the general public for it to be used as a preventative marketing ploy, then the foreigners should also count as members of the general public who are entitled to be scared. Just fobbing it off on a “it probably won’t happen” “eternity scenario” ignores the political realities behind these moves.
Alright, I’ll stop there. Let’s have a discussion. Arudou Debito
ENDS
20 comments on “Eido Inoue on improbable remote tracking of RFID next-generation “Gaijin Cards”; yet “scan-proof” travel pouches now on sale”
A version of the article I sent before. A project for this weekend!
Page, with a photo of the FCW found here: http://directactionstation.com/?p=1856
Make a Faraday Cage Wallet
From Wired How-To Wiki
You already have your tin foil hat, and you’re pretty sure no one can find you on Google, however there’s one detail you may not have thought of and that’s those pesky RFID chips.
RFID tags identifying who and — gasp! —- where you are can be found in passports, ATM cards, credit cards and some state-issued ID cards. The same technology will possibly even be used in paper money in the near future.
With the right equipment, these chips can be read from afar by data snoops or your friendly government official. A Faraday cage is sufficient for blocking such eavesdropping.
Here’s how to hide yourself from both the baddies and The Man.
This article is a wiki. http://howto.wired.com/wiki/Make_a_Faraday_Cage_Wallet Got extra tips for constructing an RFID-proof wallet? Log in and contribute your advice to this page.
1 What You’ll Need 2 How To Proceed
2.1 Step 1: Make the main pocket 2.2 Step 2: Add the metal shielding 2.3 Step 3: Make a sandwich 2.4 Step 4: Construct the billfold 2.5 Step 5: Make a credit card pocket 2.6 Step 6: Make an ID card pocket 2.7 Step 7: Test your wallet
Put your cell phone inside and close the mouth of the wallet. If it doesn’t ring when you call it, your wallet works!
Speaking of Japanese citizens and legal obligations backed up with criminal punishment,
check out the reactions of these talented individuals when faced with having to carry an ID 24/7;
http://www.dailymotion.com/video/xffp4d_arizona-omg_webcam
If only they’d knew about Japan…
— Yes, such gasps from the gallery thinking Arizona is tough (and might even target Japanese!!). Completely ignorant that this is exactly what has gone on for NJ in Japan for half a century.
Marius that clip almost made me puke.
Disgusting.
All I can say is that you have to protect yourself and if they make us carry these cards, wrap them in aluminum foil. This creates a faraday cage and is completely unreadable until you unwrap it.
I was skeptical but I tried it with my suica and it was not read in a number of locations. It sucks that this is what the world is coming to. Aluminum foil is cheap, its time to go shopping.
I also called American Express and told them to remove the ability to make purchases with the rfid chip. I also hammered the chip in my US atm card.
Paranoid? no, just making sure that I have control of my wallet.
Marius, I’m glad you have that clip. I saw that TV program when it aired. I told my girlfriend straight away that I was subjected to that very same law here in Japan. Talk about a conversation killer!
The show also talked about how the U.S. has problems because there are so many non-Americans (or rather non-White people) and it could be a big “ヒント” to Japan to not allow more non-Japanese in.
When do these RFID cards start to replace the current version?
This topic kinda has a Neo-Luddite feel to it. I say, if foreigners have to be carded, then native Japanese need to be carded too. I’d be awfully interesting to see how everyone would react.
that clip from marius made me feel physically sick as well..
the worst bit is the one where the subtitles say japanese are treated as gaikokujin in america
what a surprise it seems
A well written article. I have seen signs on buses telling people to take their pasmo out of their wallet or it won’t work because of the interference of other cards, and all other evidence I have seen on these rfids ponts in the direction of all worries being of the tinfoil hat variety.
As regards the product Debito saw, I would say it is 50% scaremongering, but it is worth remembering that many different cards have RFID chips in them these days (my company ID for one) and not all of them have the security precautions that passports and drivers licences do. (Cos they cost more money…)
One of the long term goals of RFIDs is to put them on individual products to track production lots in a more detailed way than just barcodes, and that would not be possible if they were detectable at more than a few centimeters because it would be impossible to tell one from the other.
On the other hand, this is a technology that is being commercialised, and that means that one day it WILL be hacked. But the people who will suffer first and foremost from that are the people who issue these documents (passports and ID cards), as there system security will be worthless (and they will no longer be able to implement the restrictions they want to impose), so they will be the first in line to get a stronger, more expensive replacement system. (Who says engineers aren’t business savvy?)
[Addressing these things one issue at a time. This addresses #3]
Debito, I’m not sure where you got the “required to be IDed by private businesses”. The MoJ merely published the specs making it possible for commercial enterprises to verify the digital version of the ID. It didn’t say that financial institutions and cell phone companies are required to check your zairyū card, it simply listed those two types of businesses as examples of businesses that need a secure domestic Japan ID for NJ that’s better than the ARC. It’s simply standard procedure to publish specs and methods for verifying/accessing the (both digital/analog) authenticity for identifications (and money, and precious metals like gold and platinum †), be it for non-Japanese or Japanese.
Currently, nothing really fits the bill for NJ: passports are international IDs and don’t have the info that these businesses need (eg. domestic Japan address) and has too much information on it, health insurance card and social insurance card doesn’t have photo or digital verification and are thus too easy to abuse and has too much information on it, ARC can have too much information on it and no digital verification, and a driver’s license has too high of a barrier for acquisition (ie. pass driving test) and too much information.
I’d rather give them a zairyū card (or a jūki card, which is the Japanese equivalent in terms of functionality as a digital domestic photo ID) than any of the alternatives above, which give them too much unneeded info or not enough needed info.
† My made-in-Japan platinum wedding band even has a mark on the inside of it from the Japanese mint.
— Okay, not “required” yet. But certain phone companies (such as Softbank) will certainly add it to their list of “required documents” if they feel enabled to do so by the authorities and/or technology.
In any case, I understand the need for ID in certain situations, but the point is that I want ID to be the same for Japanese and NJ. I don’t want ID to be specific and targeting NJ, due to the potential for abuses we’re seeing developing from the system as it stands now into the Zairyuu Cards.
If there are any flaws (like the ones you mentioned above) in ID for Japanese, I want them to be fixed across the board. They won’t be, because the J public will not accept IC Chip IDs carried 24/7 with criminal penalties for noncompliance. So implying (if that’s what you’re doing) that NJ should have to grin and bear Zairyuu Cards because the system for IDing Japanese is flawed is odd logic.
[This addresses concern #1. This was actually in my original FAQ but I took it out because it was too technical]
Q: So what happens when the governments “sacred encryption keys” are discovered / guessed / stolen? Can bad people read my card now?
A: No. It simply means that bad people can now forge the digital part of the identification. They still have to forge the (analog, printed parts) of the ID, including all the fancy holograms etc, and they then have to use that forged ID before the certificate tied to that key is revoked (see below). The encryption and keys that are used in the back/forth communication between the reader and the card are separate keys, are never transmitted between the two, and are different (random) for every single communication. Thus, even if the government screws up and the key ends up in bad hands, it won’t help them skim your card or eavesdrop on your card communicating with a legit reader, as these keys are separate, different (random) every time.
Possessing the “sacred keys” means that a forger will now be in the same position a 20th century forger is in: they have a chance at creating a passable ID, with bogus info, which can fool the authorities.
Q: What can a government do if its keys are stolen?
A: Fortunately, there’s a nice, well thought out system for this: PKI (public key infrastructure) allows for 1) expiration dates on issued certificates 2) a system for the revocation of certificates based on known compromised keys etc and 3) a chain of authority to allow for the re-issue of certificates. In the worst case scenario everybody’s ID needs to be re-issued because everybody’s cert is voided. This is obviously bad, but more from an inconvenience point of view as everybody’s ID is suddenly worthless from a digital point of view (fortunately, there’s still the analog printed backup) until the IDs are re-issued with new certs and the readers are programmed to recognize a new certificate authority.
This PKI/certificate stuff is the exact same thing (everybody these days, unless they’re fools, uses the same professionally vetted-over-decades industry/government standards and protocols) used on your computer to verify websites, etc., so if you click on the padlock etc of a SSL site then click on “properties,” you can see most of the basic core details (expiration dates, certificate authorities, etc) that would be on the certificate protecting the authenticity of the data on the chip.
In case you’re wondering, while keys occasionally do get stolen, it’s far more common for a government/commercial org to re-issue certs IDs because they lost (including the person(s) that know the key info dying/disappearing without passing the ti on) or accidentally deleted the key/password and/or cert.
If you lose / delete a key and it hasn’t fallen into bad hands, this is still bad (from the government/commercial org) point of view, but it’s bad because you simply can no longer make digital IDs without creating a new certificate (which can be possible without reprogramming the readers/software due to the “chain of authority” that I mentioned in #2). The government losing / deleting the master secret key does not mean your ID stops working (unless they issue a digital revocation order for your certificate).
— Can you just give us a nice tidy conclusion tying this back to the blog entry discussion points? Thanks.
Tidy conclusion? I’ll try:
The technology is sound. But there are still two weak links. These weak links are the same weak links that are present in all IDs: the humans. The government that issues the ID and the human that possesses it.
The human government officials are a weak list, but YOU, the possessor, are the weakest link. If your e-id credentials fall into the wrong hands, I would place a bet any day that it will not be because of high tech hi-jinx; it will be good old fashioned theft: your wallet was lifted while you’re intoxicated on the train, your bag will be stolen when you leave it out of your sight for a few seconds, or your ID will be photocopied while you give it to somebody and leave it out of your sight for a minute. It’s ten thousand times easier for a thief to pickpocket you than it is to get all Mission Impossible with techno-spying.
So, the digital additions to the ID help reduce the odds (but don’t eliminate) that you will be compromised due to careless human error or intentional foul play. The tin foil counter-argument to this is that the digital additions are a conspiracy by the government to spy on us more easily, and serve not to protect our information, but rather to make it easier and faster to covertly (read: wirelessly) track us. Knowing what I know about how these chips work and what’s on them, I can say that this concern is false.
A crude analogy (and response to #4): Think of each electronic security mechanism as a keyless deadbolt on your door (which represents your e-id): the BAC, the limited range, the encryption. Three quality keyless deadbolts on a door. Will a fourth deadbolt (ex. an RFID shield around the wallet) make it harder to break in the door? It won’t make the door any EASIER to break into. With brute force can they break the door down? Well, yes, but this will destroy the door (<– analogy to dissecting and/or reverse engineering the ic chip to try to extract the information on it).
My concern is so many people obsess over that fourth deadbolt (all that tin foil) because they're convinced that somehow people will get by those three locks (or they don't know they already have three locks) is that they forget about that extremely easy-to-break-into weakly locked window behind their house (<– an analogy to having your bag/wallet stolen or pickpocketed) Or the bad person, knowing the futility of trying to get past the 3/4 deadbolts, is going to take an axe, ignore the deadbolts, and chop down the wall next to the door.
— Thanks very much, Eido. I appreciate this discussion very much. My conclusion is pretty much the same:
Technology keeps getting invented and pushed by boffins that tell us not to worry and learn to love The Bomb. Don’t worry. If there will be any technological problem, it’s not with the inventors or the dispersers, it’s with the users. Guns don’t kill people, people kill people, after all. But remember, the focus of this blog entry has been: It’s not all the people being affected by this. It’s only people who have no real political power in this society to protect themselves — the foreigners. Because the rest of J society doesn’t want to be treated and tracked like criminals constantly, they won’t be. Instead, they force upon the NJ the technology that encourages identity theft. Calling the humans who have to carry this technology in their wallets “the weakest link in the chain” ignores the issue that it’s not them who’s asking for it. So once identity theft happens, it’s probably their fault as the possessor? Sorry, I don’t follow. But it’s within character for the inventors — hey, we’ve taken all sorts of measures to protect you, so don’t you dare do something stupid to void that protection. That’s not how I see the issue. They shouldn’t be put in this position in the first place.
Anyway, thanks again Eido. Appreciate all the information and the informed discussion.
Happened across this link too: http://chipblockers.com/
This is maybe a little off topic, but for cell phone companies and banks to stop taking non-photo ID, Japanese citizens would also have to be required to get one of those juuki cards. I don’t think a very big percentage of the population has them as of now.
It may not be a photo ID, and at least in my case my address is handwritten on the back (by me, so there’s no way to tell if that’s my actual address), but if it becomes impossible to use a health insurance card in the future, that’ll eliminate the one way to prove your identity WITHOUT specifying your nationality, Japanese or not. If only Japanese have juuki cards and only NJ have zairyuu cards, that perky little jr. college graduate at the Softbank shop is going to have instant, obvious access to a VERY important piece of “kojin jouhou.” Nationality definitely falls into the same category as head of household or honseki or place of birth… unless the person looking at the ID is an immigration officer, it’s none of anyone else’s business. We need an ID that doesn’t specify.
I’m also troubled by the fact that there’s no confirmation of an alias being listed. Could you imagine if Japanese who lived in the US (or any country that uses the roman alphabet) were only allowed to hold ID with their name listed in kanji that no one can read? Of course most Japanese will say that in Japan, people know the roman alphabet so it’s not the same issue… but it absolutely is. Just knowing how to sing the ABC song doesn’t mean that you can pronounce any name in the world, and again, being able to tell someone’s nationality based on the alphabet that their name is written in gives people who have NO business knowing their customers’ nationality access to very sensitive information.
Kimberly, your second point is a very important one.
I myself don’t have a driver’s license, so I’d ilke to hear from someone that does: is it truly required that people with foreign nationality have their alphabet name on the front of their license, and not the katakana version (or an official katakana alias)? If this is the case, then the removal of the line indicating honseki (or, for NJ, home country), has done very little to improve the privacy of the license for non-Japanese, because it would mean that while the specific nationality is no longer indicated, the fact that the holder’s nationality is something other than Japanese is now able to be deduced — names in kana/kanji are Japanese nationals and names the alphabet aren’t.
I’ve been trying to use a single, standard katakana form of my name, last then first, as much as possible in official contexts. My bank accounts are in this name, my property is held in this name, my utilities contracts are in this name, and my hanko is in this name (surname only).
This is a bit off-topic (though it relates to your first point), but when I signed up for my mobile phone contract with Softbank a few months ago, I was able to get the best possible payment plan (no money up front, no credit card; monthly bill deducted automatically from my bank account) without revealing my nationality and in fact using the least personal-info-revealing ID possible. I used the health insurance card and (IIRC) my proof of having paid property taxes in the previous year. You can use another utility bill also. Together they established my address, and at no point did I have to reveal my nationality.
When I got the phone call soon after saying that my application had been approved, with payment plan as I had selected, I was pleasantly surprised enough to go cancel my old Docomo contract and get my Softbank iPhone the same day!
The ability to use a property tax payment receipt as ID is much fairer and more open than a driver’s license — no legal resident is forbidden to own property (and thus pay property taxes, and get a receipt for those taxes), whereas there are physical limitations (for example, only people with vision above 0.6 in one or both eyes) on who can obtain a driver’s license, and people who don’t meet those requirements are forbidden from having one.
And those tax/utility bills are printed on ordinary paper, with no place to hand-write amendments, so (to bring this back on topic, somewhat) you can use them as ID without any fear of having personal data compromised!
is it truly required that people with foreign nationality have their alphabet name on the front of their license, and not the katakana version (or an official katakana alias)?
When I got my first Japanese license, they printed my name in alphabet on the front and printed the katakana transliteration (registered alias) as an endorsement on the back, but they asked me if it was OK to do this first, so I may have had the option to put katakana on the front. I just renewed my license this week and the new license does not have my katakana name at all, nor did they ask me about it.
A South Korean co-worker of mine had a Japanese driver’s license with his kanji name on the front, but I am not sure whether that is because it was his legal alias or because it was his legal name in Korea and in his alien registration.
Two asides: The latest Tokyo licenses have no printed honseki/nationality field at all, in contrast to the blank field that appeared on all driver’s licenses for the first couple of years after IC chips came out. The honseki/nationality is still stored on the IC chip (you are asked to verify it on the IC reader before leaving the DMV) and supposedly can only be read by the police, because private firms can only use IC readers to check the information on the card against the information inside the card. There is also now a space on the back to specify whether you want to be an organ donor, which I definitely like.
@Mark in Yayoi
You can take it one step further like I did:
Have a KANJI nickname put on your ARC, and then
Have that Kanji nickname put on your Health Card!
Boom, you’re Japanese on paper, and that Health Card is a very official “paper”.
Suddenly, you’re not marked with “Kata(this-is-a-gaijin)Kana” anymore, now you have a 100% Japanese Kanji name, you can avoid a lot of racist practices.
The Japanese people who look at my Health card (whether it be when applying for a credit card by mail, or simply when at the dentist) all assume that I’m a Japanese citizen.
With Kanji, when doing things by mail, people receiving applications from me now assume my DNA is, ahem, the “right” type, and so they approve things and operate as normal.
With Kanji, when doing things face-to-face, people see I’m the “wrong” type, but they assume I must have gone through the process of becoming a Nationalized Japanese, and thus they assume I have the legal rights of an “actual” Japanese Citizen, and so they treat me as they would an “actual” member of the group called society.
(No doubt some say to themselves, “Kuso… I’ve gotta’ treat this foreigner fairly, like a Japanese person? Damn. We really need to make a law that prevents this kind of thing: Foreigners becoming Japanese Nationals, it’s an abomination I tell ‘ya!”)
It’s really amazing that I managed to get this Japanese Heath Card printed up with 100% Kanji: this card is a highly respected form of identification for ware-ware Nihonjin (heh-heh).
“Katakana: a special set of letters to used to mark all foreign words and foreign PEOPLE as being OUTSIDERS FOREVER. It’s great. You’ll love it!”
I tell Japanese folks, “Imagine you go to America, and they say something like this: ‘Welcome to America, but because you have Japanese DNA you can’t use the Roman Alphabet, sorry, Japanese people are not allowed to use the Roman Alphabet. America has now created a racist “Foreigner Alphabet” just for you Japanese people, because we want to know who is American (we must be fair to Americans) and who is Japanese (we don’t have to be fair to Japanese.) Japanese have no legal rights in America. Sorry. So from now on, to make it easier for us to commit Racial Discrimination against you, in every transaction, you must always mark yourself with this “Outsider Alphabet.’ What do you think about that?”
Too Long: Don’t Read
Basically the above post is suggesting you Kanjify your Health Card bro.
But you’ve got to be a smooth talker when you do it. Some Health Card officials might refuse to print you a Kajified Health Card.
I don’t know if this is a legal-right everyone can successfully claim, or if this is just a lucky-privilege I managed to grab using a combination of confident body language, positive facial gestures, polite yet authoritative words, friendly yet hurried and expectant vibrations, and luck?
Perhaps sharing this experience here on Debito will spark a mass flood of foreigners walking into the Health Card sections of their local City Halls demanding Kanjification.
I’m sharing this info altruistically, so remember, if 6 months from now, due to an overwhelming number of “Foreigners passing themselves off as Japanese (gasp) using Kanjified Health Cards”, if Japan were to decide to pass a law against my Kajified Card, and if City Hall were to then revoke my wonderful Kanjified Card, then… I think you guys and gals will owe me a drink. (But don’t worry, you can pay for it using that nice new Credit Card you received in the interim thanks to the fact that the bank was fooled into thinking you were Japanese since you applied using that Kanjified Health Card before it was outlawed! [High Five!] 🙂
— Related topic: In my case, when I go to my favorite kaiten zushi restaurant (it’s usually full, so we give our names and wait), I watch to see how they render my name. As a policy, everyone gets rendered in hiragana. However, if they dare to put my name in katakana, I say, hang on, call over the manager, ask why I alone am being rendered in a different script (well, duh!), get an apology, then leave (there’s a perfectly good gyoza restaurant just four doors down).
This has happened two times so far. However, the second time I admonished the manager that won’t I come back ever if it happens again (three strikes and you’re out). It hasn’t happened again.
PS – After receiving my Kanjified Health Card, I used it to easily effortlessly change my cell phone account at AU, and my bank accounts at 3 different banks, including JP (and I didn’t let them get away with putting a line through the old Romaji/Katakana name and writing the new Kanji name underneath that by hand, nope, I got all 3 banks to print up FRESH Passbooks for me, with 100% Kanji being all you can see.
And, I might add, the Kanji I chose are totally rad. 🙂
PPS – I’ve found that you can even further push the Japanese person you’re dealing with, into making the assumption that this Kajified Health card means that you’ve become a Nationalized Japanese Citizen:
As you slap the Kanjified Health Card onto the table release a big smile from the heart (as if you were just recently granted Japanese Citizenship successfully) and announce, “Nip-pon, Cha-Cha-Cha!” 🙂
It pays not to be overly technical with these issues because most people, including Japanese people, have no idea how their own country’s immigration and nationality laws work.
For instance, when I went to rent my current apartment, the landlord asked whether I had permanent residence. I don’t, but I am a seishain at a big company which always renews my residence permit, and this is (in my view) exactly the same as PR from a counterparty risk perspective, so I said “基本的に同じような資格を持っています” and the landlord said OK — even after photocopying my alien card.
I bet that if you show a romaji ID (other than a gaijin card) in a bank or cell phone shop and say you’re a Japanese citizen, nobody will bat an eyelash. They have no way to argue with you unless they know the naming rules, and I seriously doubt that anyone in the private sector is particularly trained to recognize that a romaji name equals foreign nationality, nor would they have any reason to know that unless they had personally naturalized from overseas.
Well, dang Steve, I was thinking I would get my name after I married someone(whether they be Japanese or not), but putting it that way, it might just be easier to make a name pretty much as soon as I land and then just change it later.
Latest snooping figures – 66 meters
http://www.theregister.co.uk/2010/08/02/long_range_rfid/